Dark Web Cybercrime and Threats: Why It Matters to Organizations
Dark web cyber threats are no longer isolated or difficult to access. They are part of an organized cybercrime ecosystem actively targeting organizations.
Cybercriminals prefer operating on the dark web because it enables anonymity, coordination, and access to a global marketplace of tools, data, and collaborators. From stolen credentials to initial access brokers, many attacks begin with signals that appear externally before a breach is detected internally.
These indicators are often missed by traditional security programs that are focused on activity inside the network. Organizations need visibility into threats that exist beyond their firewall, including activity across the surface, deep, and dark web. Industry reporting, including research from SANS, shows many organizations still lack this external visibility.
What is the Dark Web and How Do Criminals Use It?
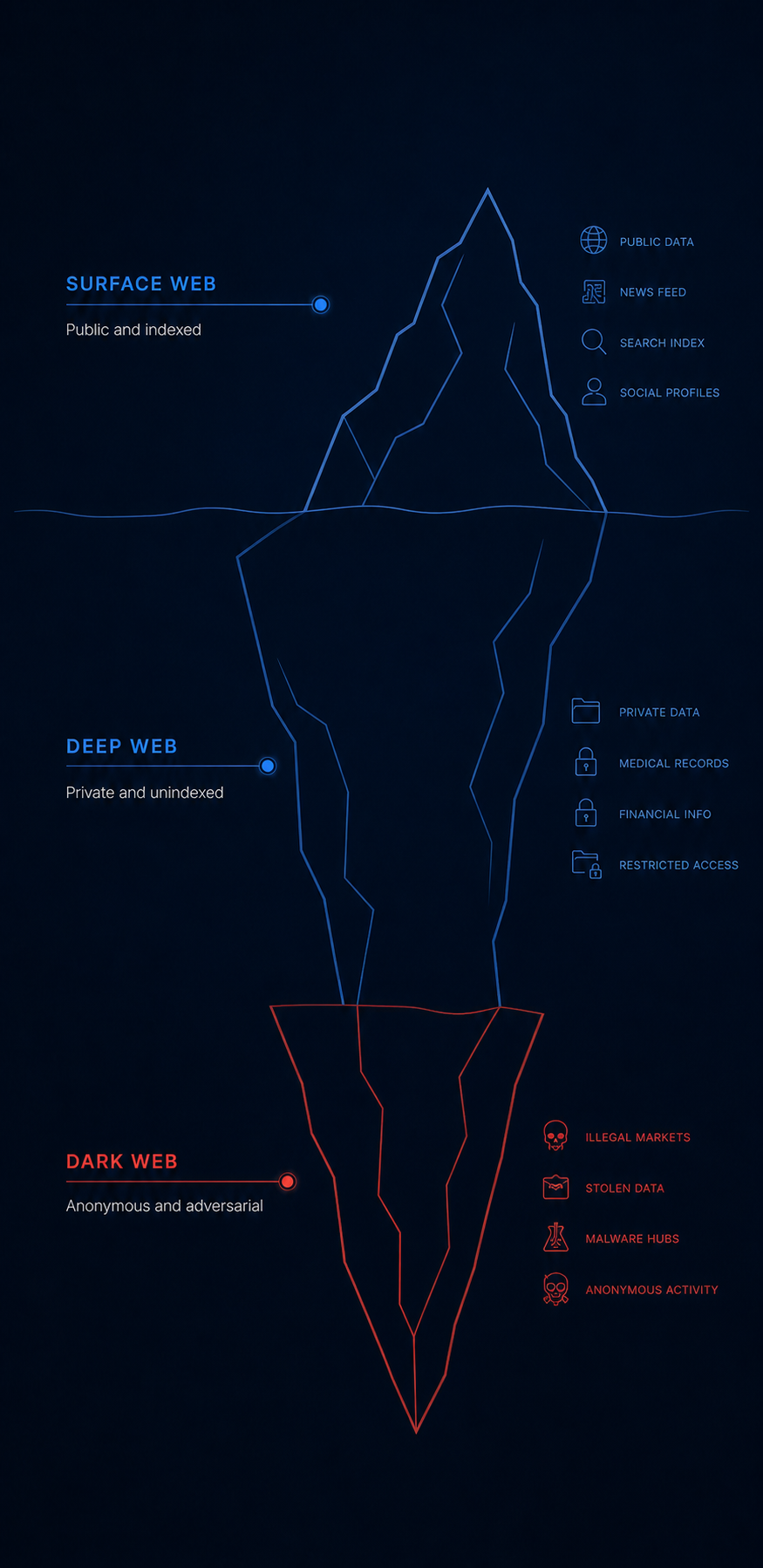
The dark web is a portion of the internet that is intentionally hidden and requires specialized tools to access. It is not indexed by traditional search engines and is designed to support anonymity.
It exists within the broader deep web, which includes content not publicly indexed such as private databases, webmail, banking platforms, and subscription-based services. While most of the deep web is legitimate, the dark web is where anonymity is frequently leveraged for illicit activity.
Cybercriminals use the dark web to coordinate, communicate, and transact with reduced risk of attribution. It functions as a marketplace where threat actors buy and sell stolen data, trade access to compromised systems, and share tools that enable cyber attacks.
How the Dark Web Enables Anonymous Activity
Dark web access relies on anonymizing networks that obscure identity and location by routing traffic through multiple nodes. This layered approach makes it difficult to trace users or attribute activity.
This is one of the primary reasons cybercriminals prefer operating on the dark web. It allows them to validate access, exchange data, and coordinate attacks while minimizing exposure.
For organizations, the concern is not how these environments work, but how they are used. Anonymous access enables the exchange of stolen credentials, exploits, and network access that can directly impact employees, systems, and third-party relationships.
How Cryptocurrency Enables Dark Web Cybercrime
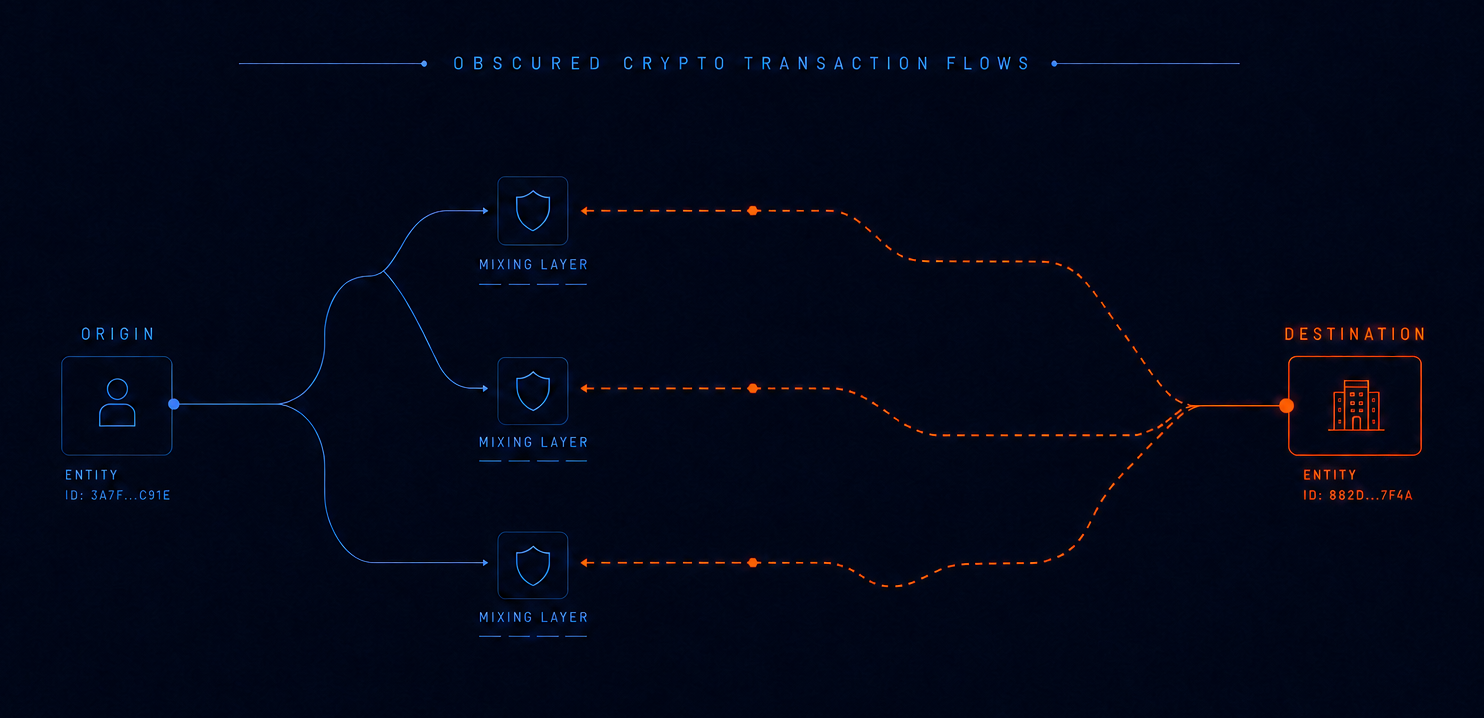
Cryptocurrency enables fast, decentralized, and pseudonymous transactions between threat actors.
Unlike traditional payment systems, it allows funds to move across borders without centralized control. This makes it the preferred method of payment for stolen data, access listings, ransomware, and fraud services.
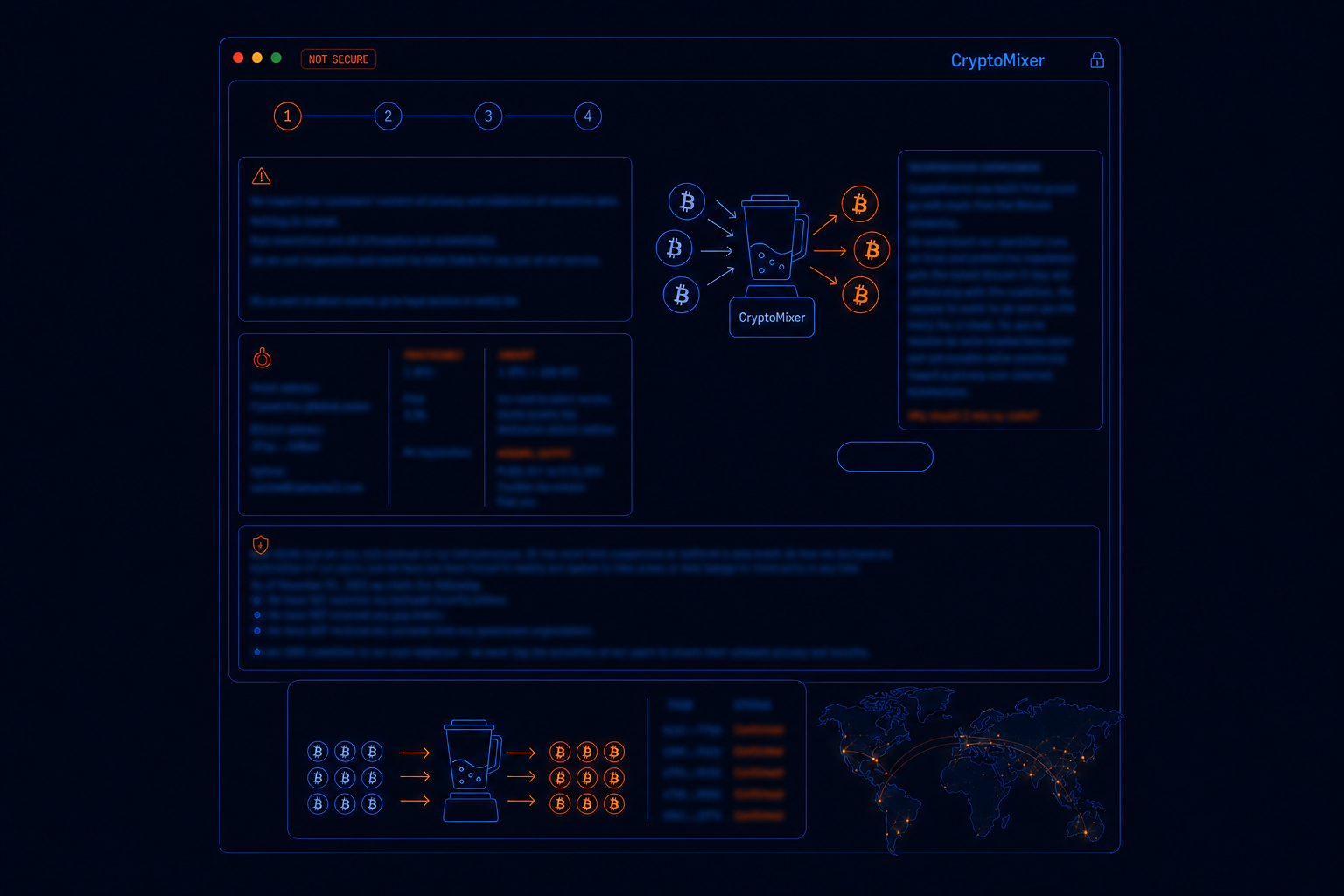
Although transactions are publicly recorded, threat actors use mixing services to obscure financial trails and reduce traceability. These techniques function similarly to traditional money laundering, allowing cybercriminals to operate at scale.
What Happens on the Dark Web
Common Dark Web Cybercrimes Targeting Organizations
Dark web cybercrime is structured and targeted. Threat actors actively focus on organizations through the sale of access, data, and attack capabilities.
One of the most significant risks is the sale of access to corporate environments. Threat actors trade stolen credentials, validated VPN access, and other entry points that can be used to infiltrate networks. These transactions often occur before an organization is aware of a compromise.
Other common forms of cybercrime include:
- Credential theft
- Intellectual property theft
- Ransomware operations
- Fraud services
These activities are interconnected, forming a supply chain where one actor collects data, another validates access, and others execute attacks.
Dark Web Marketplaces and Cybercrime Activity
Dark web marketplaces are central hubs for cybercrime. These environments allow anyone to buy, sell, and exchange illicit goods, including stolen data, access credentials, and fraud services.
Unlike traditional criminal networks, these marketplaces operate at scale and are often crowdsourced. Threat actors can quickly monetize stolen information or purchase tools needed to execute attacks.
For organizations, these marketplaces provide early indicators of exposure. The presence of credentials, access listings, or brand-related discussions can signal ongoing or impending risk.

Common Cybercrime Activities on Dark Web Forums
Dark web forums and marketplaces support a wide range of cybercrime activities that directly impact organizations. These environments are not only transactional but also operational, enabling threat actors to refine and scale their methods.
Carding and Financial Fraud
Stolen payment data and financial accounts are used in coordinated fraud schemes. These operations often rely on phishing, social engineering, and techniques designed to bypass authentication controls.
Fraud Techniques and Tutorials
Guides and services teach threat actors how to bypass security controls, exploit platforms, or execute refund and impersonation fraud. This lowers the barrier to entry and accelerates the spread of attack techniques.
Cryptocurrency Laundering
Mixing services and tumblers obscure transaction trails and make it difficult to trace funds back to their origin.
Fake Identities and Account Creation
Threat actors create synthetic identities and fake accounts to regain access to platforms, conduct fraud, and maintain persistence after removal.
These activities often signal broader cybercrime operations when linked to organizational data or access. The challenge is in identifying the threat actor behind the synthetic identities.
Related: How Nisos identifies the person behind the persona.
Who Is Driving These Threats
Threat Actors Driving Dark Web Cybercrime
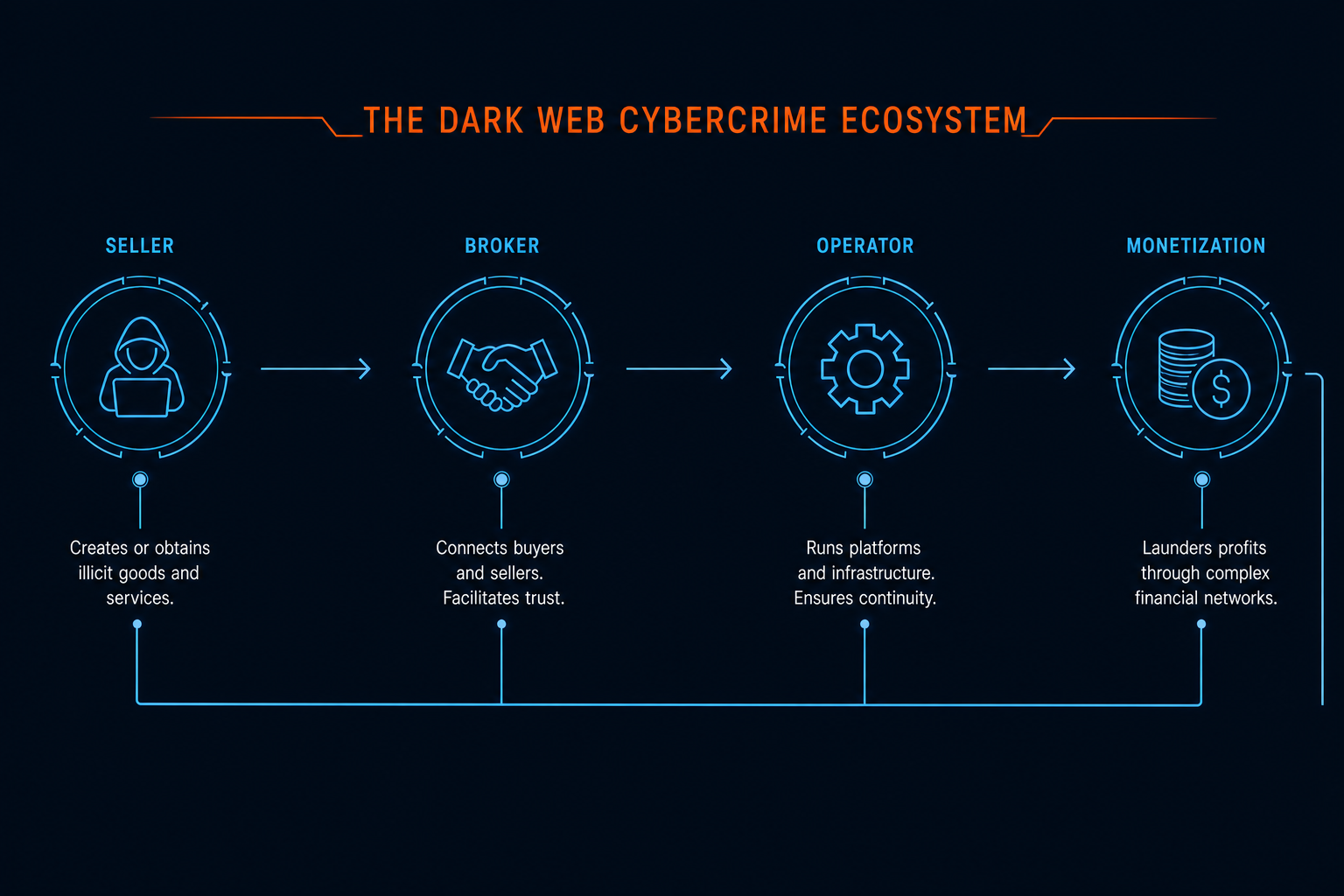
Dark web cybercrime operates as a structured ecosystem where different actors specialize in specific roles.
Sellers
Distribute stolen data such as credentials, financial information, and personal identities.
Initial Access Brokers
Identify and validate entry points into corporate environments, including VPN and remote access credentials. These access points are then sold to other actors, often before organizations detect a breach.
Exploit and Tool Developers
Create malware, phishing kits, and exploits that allow attacks to be carried out at scale.
Technical Operators
Execute attacks by moving laterally within networks, escalating privileges, exfiltrating data, and deploying ransomware.
These roles form a cybercrime supply chain where one actor’s output becomes another’s input.
Why This Matters
Where Human Risk Comes Into Play
Dark web cybercrime ultimately targets people.
Executives are targeted for impersonation and fraud. Employees become entry points through compromised credentials. Third-party partners introduce risk through exposed data and hidden vulnerabilities.
Understanding who is behind these activities, and how they connect to real individuals, is critical for interpreting threats and determining risk.
Key Use Cases for Monitoring Dark Web Activity
Monitoring dark web activity provides visibility into threats that are not detectable through internal systems.
Cyber Threat Intelligence
- Identify exposed credentials
- Detect malicious infrastructure and exploits
- Monitor ransomware and phishing activity
Physical Security Intelligence
- Identify exposed personal data
- Monitor threats targeting employees or executives
Platform and Fraud Intelligence
- Detect account takeover and fraud activity
- Identify misuse of credentials
Reputation Intelligence
- Monitor discussions involving your organization
- Identify reputational risks
Third-Party Intelligence
- Detect supplier breaches
- Identify downstream exposure risks
Why Traditional Security Controls Are Not Enough
Traditional security controls are designed to detect activity inside the network.
Dark web cybercrime develops outside that perimeter. Threat actors exchange data, validate access, and coordinate attacks before activity becomes visible internally.
This creates a gap between when threats emerge and when they are detected.
How to Monitor Dark Web Cyber Threats
Effective monitoring requires identifying relevant signals, understanding context, and determining risk.
Continuous External Monitoring
- Exposed credentials and sensitive data
- Mentions of your organization or executives
- Data leaks involving employees or third parties
- Emerging threats and access listings
Targeted Threat Investigation
- Analyze activity linked to specific users or incidents
- Validate access listings or data leaks
- Identify threat actors behind activity
- Connect external signals to internal risk
Monitoring combined with investigation allows organizations to prioritize threats and act before they escalate.
Reducing Risk from Dark Web Exposure
Organizations must reduce the likelihood that exposed data can be used against them.
Key measures include:
- Strong credential management
- Multi-factor authentication
- Monitoring for misuse of personal or financial data
These controls reduce attacker success and limit the impact of exposed information.
Understand the Threats Before They Impact You
Dark web cyber threats develop outside your organization, long before they are detected internally.
Nisos helps organizations identify, monitor, and investigate these threats across the surface, deep, and dark web. By combining continuous monitoring with analyst-led investigation, we provide the context needed to understand risk and take action.
Frequently Asked Questions (FAQs) on Dark Web Cybercrime and Threats
What is dark web cybercrime?
Why do cybercriminals prefer operating on the dark web?
What types of cybercrime occur on the dark web?
Common types of dark web cybercrime include:
- Credential theft and account takeovers
- Sale of corporate network access
- Ransomware operations
- Financial fraud and carding
- Identity theft and impersonation
How can organizations detect dark web threats?
Organizations can detect dark web threats by monitoring for:
- Exposed credentials and sensitive data
- Mentions of their organization or executives
- Data leaks involving employees or vendors
- Listings advertising access to their systems
This requires visibility beyond internal systems and into external environments where threats originate.
