Blog
Russia Isn’t the Only Nation State Threat Actor: Keep an Eye on These Three Nation States
The Russian aggression against Ukraine is no secret. It has certainly been getting a lot of airtime lately. Everybody seems to have written a blog or a white paper. Heck, even we did. In our recent blog, Russian Aggression and Its Potential Impact on the West, we outlined the ways we believe Russian state actors could eventually reach and impact western enterprises and businesses. While it is wise to keep an eye on what’s happening in Russia, there are other active nation state actors out there that pose a significant threat to western organizations. Some may use the fog of war to their advantage. Ignore them at your own peril.
Active Nation State Cyber Actors
We believe the following are the top three foreign threat actors and nation state adversaries. They have the strongest computer network exploitation capabilities and they use them to target Western interests with disruption, e-crime, and espionage.
- China: While we don’t believe that China will use destructive capabilities in 2022, we do think they will continue to be involved in long term computer network exploitation and insider threat recruitment activities to steal intellectual property. We believe the targeted IP theft will be centered around technology/artificial intelligence, pharmaceuticals, biotechnology, manufacturing, and chemical-agro industries. Based on recent rhetoric, we assess the current Russian and Ukrainian conflict may embolden China and lead them to be more aggressive in Taiwan. When that happens, we are bound to see more aggressive regional cyber attacks and disinformation campaigns in furtherance of their anti-Taiwan goals.
- Iran: We have seen more aggressive tactics from Iran throughout 2020 and 2021 and we think they will continue to utilize their cyber tools in an aggressive manner. CISA.gov states that, “They continue to engage in conventional offensive cyber activities ranging from website defacement, spear phishing, distributed denial-of-service attacks, and theft of personally identifiable information, to more advanced activities—including destructive malware, social media-driven influence operations, and, potentially, cyberattacks intended to cause physical consequences.”
CISA explains that the most recent Iran cyber threat actors, known as MuddyWater, are a group of Iranian government-sponsored APT actors conducting cyber espionage and targeting a range of government and private sector organizations, including those in Asia, Africa, Europe, and North America. - North Korea: The North Koreans have been conducting cyber theft against financial institutions and cryptocurrency exchanges worldwide. It’s been speculated they are stealing huge sums of money in an attempt to fund government priorities including nuclear and military programs. In the 2021 Annual Threat Assessment of the US Intelligence committee report from the Office of the Director of National Intelligence, it is stated that Pyongyang likely possesses the expertise to cause temporary, limited disruptions of some critical infrastructure networks and disrupt business networks in the United States.They are also likely able to conduct operations that compromise software supply chains. Also, based on their past cyber attack development cycles, that may indicate that they likely are working towards developing this into something more far reaching. If they apply the capabilities they are using to attack financial institutions to technology acquisition closer to their end goals, the energy and military/government contractor, or even the commercial space technology sectors, may end up becoming their next targets.
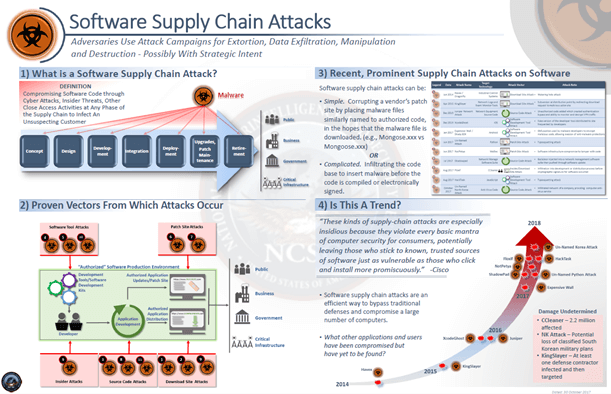
Image source
What Questions Should CISOs Ask About These Nation State Actors?
CISOs need to be aware of threat actors in Russia, China, Iran, and North Korea. World politics play a huge role in the strategy and level of aggression we may experience. To keep things in context, here are the 5 questions you should consider when preparing your enterprise for potential attacks:
- When will Russia attack Western businesses more aggressively and what will the damages be? The answer to this will provide you with a tentative timeline for preparation and actionable steps to mitigate damages.
- At what point will Russian nation state efforts intertwine with Russian ransomware gangs and deliver increased ransomware attacks?
- Taiwan continues to be the most contentious issue in the U.S.-China relations. Will Taiwan step in to respond to the Russian invasion of Ukraine? If so, how will this impact the relationship between China and the United States?
- How will China’s cyber, disinformation, and insider threat recruitment efforts change if they become more aggressive towards Taiwan?
- What will be the scale of these efforts, what industries will be targeted, and how will that impact enterprises directly and through their supply chain?
How Does Threat Intelligence Provide a Better Defense?
Threat intelligence plays a significant role in implementing a risk-based approach to enterprise threat management for both cyber and physical security. Threat intelligence, threat hunting, open source monitoring, real-time alerting, and investigative responses to tailored questions should inform the appropriate risk based approach to cyber security, physical security, supply chain risk, insider threat, disinformation, brand reputation, and fraud.
A comprehensive analyst-led approach, that provides organization-specific data, context and recommendations, will help security teams quickly prioritize not only the proper controls, but also put policies in place that provide positive outcomes to any potential disruption. In addition to controls, organizations should focus on disrupting the threat networks, blowing their cover, attributing the actors, notifying law enforcement and the intelligence community, sharing with industry partners and researchers, and warning the broader global community.
About Nisos®
Nisos is The Managed Intelligence Company®. Our services enable security, intelligence, and trust and safety teams to leverage a world-class intelligence capability tailored to their needs. We fuse robust data collection with a deep understanding of the adversarial mindset delivering smarter defense and more effective response against advanced cyber attacks, disinformation, and abuse of digital platforms.
