Blog
An Inside Look at Advanced Attacker TTPs and the Danger of Relying on Industry-based Threat Intelligence
Many organizations use threat intelligence from industry peers to prioritize vulnerability management and assign criticality when there is not enough existing information directly about their organization or their organization’s critical assets. While this is a natural political response to frame the narrative to allow budgetary approval to build certain aspects of the security program, organizations need to defend specific to their own technology stack and assets, incorporate the proper tooling around this stack, and be able to log events at scale.
If a security program indicates that their industry peers are being targeted by a variety of different threats broken down by industry, the narrative around this argument will likely be a more persuasive argument for non-technical business executives approving budgets.
Unfortunately, cyber criminals and nation state adversaries simply don’t care what vulnerabilities are relevant on an industry level.
Criminals are simply looking for vulnerabilities that can make them the quickest profit in the least amount of time. While nation state adversaries may care about certain defined institutions or industries based on geopolitical considerations, they take the same approach of looking for the easiest path of resistance to gain internal access.
Security teams often do not understand the speed at which attackers pivot to exploit vulnerabilities as long as it gets them to their objective.
Further, many organizations use technologies that scale the MITRE ATT&CK framework and generally write signatures for each example such as hashes, domains, and IPs, vice the actual full techniques themselves. Alerting on Yara rule signatures alone will be grossly insufficient. Organizations need to consider that MITRE techniques often have numerous sub-categories that need alerting on behavior and not necessarily signatures.
A Sophisticated Attacker’s Infrastructure
Let’s take an example of a nation-state level infrastructure design for computer network exploitation (CNE):
Advanced adversaries source equipment to build generally four distinct infrastructures, as detailed below, through which they can conduct advanced cyber operations. Segmentation of these networks is critical to its function, and will prevent detection and compromise by advanced commercial security programs.
Nation state adversaries consider handoff between phases as the most vulnerable point in any operation. They use code segmentation in all tools – there are not any hard-coded or baked-in references to other segments meaning they build logic which phase to execute next on target instead of pushing from the server and having the code live in memory for a short time.
Memory-only code that advances the program to the next phase is generally sent by the server upon successful completion of the current phase. Once the code is successfully loaded from the next phase, the previous will zero as much of itself as possible in memory, and unload (failure to do so will greatly increase chances that commercially available security tools will detect the adversary’s efforts).
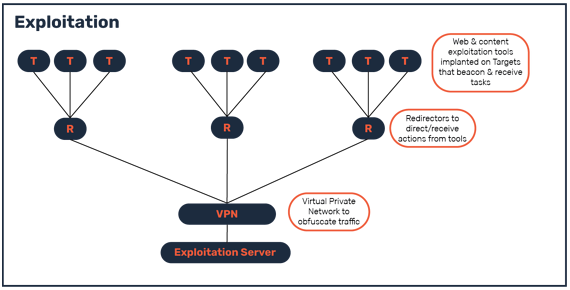
1. Exploitation Network
This network is used to gain footholds into targets via web (flash, emails) and content (PDFs, Macro viruses) exploits. Future efforts could involve advanced techniques, such as client-side browser exploitation.
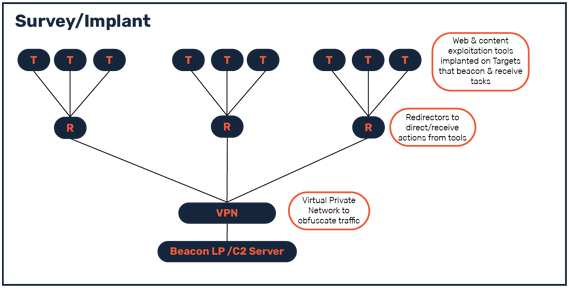
2. Survey/Implant Network
This separate network is used to expand the initial footholds via lateral movement and escalation to establish persistence in targets.
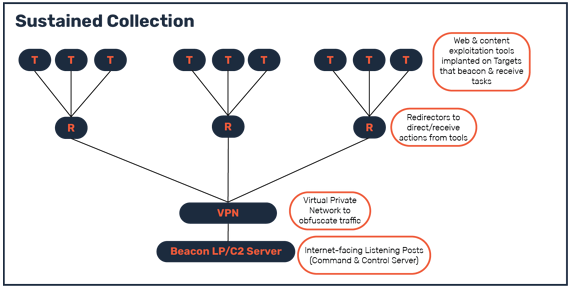
3. Sustained Collection Network
This distinct network is used to continuously collect information on targets with persistence.
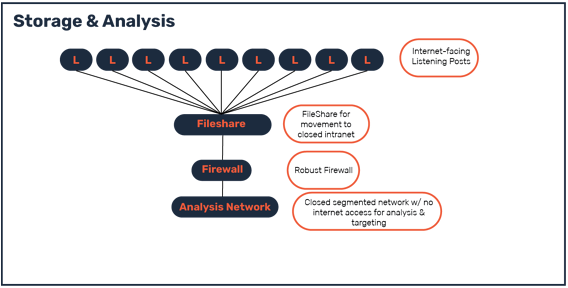
4. Storage & Analysis Network
This closed network is used to store and analyze collected information, and is not connected to the Internet. This will facilitate the production of intelligence reports for further operations.
A Sophisticated Attacker in Practice
An advanced attacker will often try to blend into the noise, attempting to appear like a common criminal group in order to gain intelligence about the response time and procedures of an organization. If, in the meantime, they are able to obtain data of value to them, all the better. Once they are caught, they might try again using the same, more disposable, middle infrastructure. They make noise in order to test your defenses, and try to operate as close to the tripwire line as possible.
Once internal access is obtained, they will not find themselves at their collection objective and will have to make various lateral movements that may cause alerts in the environment.
Lessons for the SOC
Therefore it’s critical for a security team to install and configure proper tooling to flag these movements and more importantly, that the appropriate logging is occurring over longer periods of time to be able to conduct more analysis and quickly determine if it’s a real threat or false positive.
It is also important to maintain complete records of activity on hosts in a network. For example, it is not enough to record the starting and stopping of a service. The SOC also needs to log the user account that created it, the time of day it was created, and any activity on the system that followed the potentially malicious service.
To trigger the proper alerting, many organizations make the mistake of signaturing the examples of a technique located within the MITRE ATT&CK framework. This is a problem because oftentimes there are sub-categories within sub-categories of the MITRE ATT&CK techniques that are not considered by these signatures.
Advanced attackers will often resignature tooling before swapping out middle infrastructure, so it is not simply the metadata associated with the process that is important, but also the order of execution of the suspicious activity.
It is important to not merely flag lsadump or mimikatz, but also to explicitly identify processes that sequentially read the memory of the lsass.exe process, and then follow what they might do with the data, whether it is generate more network traffic to the internet, write it to disk, or attempt to utilize enumerated credentials on the network.
Once such a sophisticated attacker determines that their actions have been caught, their next step will be to dispose of the redirector infrastructure. They may then attempt to restart the cycle. The key is trying to examine netflow in order to identify any patterns that both infrastructures have in common.
Ultimately, the focus ought to be identifying what activity on your network is normal, and monitoring for any aberrations, not simply examining signatures of an attack that was identified in another organization.
Attackers will change their behavior and signaturing slightly for each new target. Therefore, focusing only on signatures from industry is like a bank installing metal detectors, in fear of a robber with a limp who is known to wield a lead pipe. They are likely to get robbed when the thief limps in with a wooden Louisville Slugger. They should have identified more disparate behaviors of the potential attacker, but instead chose to signature him based on his weapon of choice.
